Home Lab: Enterprise Network
Home Lab: Enterprise Network
Home Lab: Enterprise Network
Overview
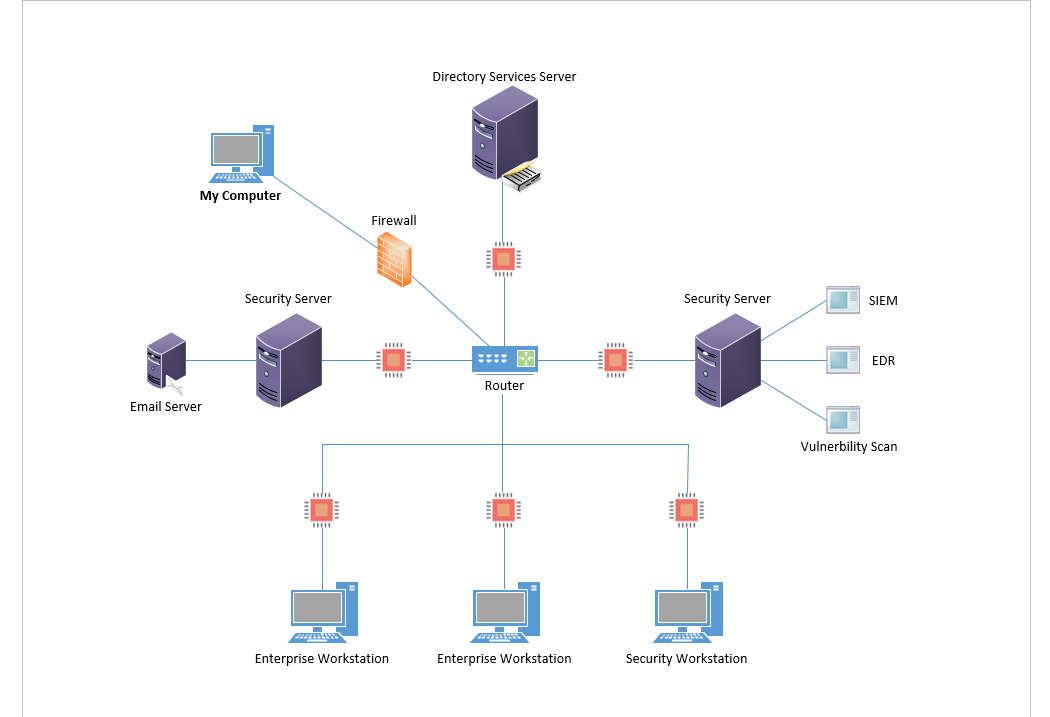
This project is a fully simulated enterprise network built in my home lab using VirtualBox. It includes multiple virtual machines simulating real-world business infrastructure such as Active Directory, email services, Windows/Linux clients, and security monitoring tools like Security Onion and Wazuh.
The environment was designed to practice:
- System administration
- Network segmentation
- Red/blue team operations
- Security monitoring and incident response
- Vulnerability assessment and hardening
Objectives
- Simulate a small-to-medium-sized enterprise IT infrastructure.
- Practice configuring domain services, email, client systems, and attacker scenarios.
- Perform basic red team (penetration testing) and blue team (detection/monitoring) exercises.
- Prepare for real-world SOC, sysadmin, and cybersecurity analyst roles.
Red Team Activities
- Brute force login attempts using Hydra
- Exploitation of weak credentials via Evil-WinRM
- File enumeration and lateral movement attempts
- And more attacks listed in the project
Blue Team Activities
- Traffic and alert monitoring using Security Onion
- Log analysis using Wazuh and Kibana
- Event correlation from multiple systems
- Practice with incident response
Lab Writeup:
What I Learned
- Configuring and managing domain services in Windows Server
- How endpoint misconfigurations can be exploited
- Using network and endpoint detection tools like Security Onion and Wazuh to monitor real threats
- Understanding the attacker mindset and linking behavior to detection logic
- Importance of segmentation, logging, and least privilege in network security
This post is licensed under CC BY 4.0 by the author.